The basic optimizations that everyone forgets
 The design looks good and promising and you are about to make it live. But wait, the job does not end here.
The design looks good and promising and you are about to make it live. But wait, the job does not end here.
Do you like to own a website that people cannot even find easily while surfing in Google?
You definitely not like the idea of owning a website that comes with barrage of problems. You can not even think of it right. But, it happens.
Even after taking so many precautions, you eventually find that you have missed out on some vital points that create big issue with your website�s online visibility. Here, we are going to share some basic seo techniques that you should not give a miss no matter what.
Meta tag: Just keeping the name of your website in the title is not going to help you make your website appear in some related search queries. You need to add some keywords in the title and Meta description sections of your website if you are to see your website getting a descent amount of traffic to targeted keywords. Do not stuff keywords in title and Meta description section as it will be treated as spam and your website might get penalized for that. Just try to keep it simple and natural.
Set Canonical: Google still treats www and non www version of a website as different URLs and that means, if URLs of your website are not getting redirected from non www to www version, it is creating internal duplicate content. This will certainly not augur well for the visibility of your website. To fix this issue, all non www URLs of the website need to be redirected to with www version via 301 permanent redirection.
Cross Browser Compatibility: This is another vital issue. You do not like to see your website opening like hell in IE because of poor cross browser compatibility issue. Now, before your make your website live, you need to check that the website is rendering perfectly in all major browsers. A poor browsing experience can ruin all your chances of making it big in the virtual world, so give it your best shot if you do not want to face an embarrassing situation at the end.
Validation: You need to make sure that your website conforms to the rules set by W3. Besides that your website does not have any error within it. Some common errors are missing alt tags, forget to close tags etc. Before making your website live, you should check them all otherwise, it will be a huge downer for both the users and search engines.
Analytics: Do not forget to add analytic codes in your website. Without them you will not be able to get indepth analysis of your website. Just create a Google Analytics account and there you go.
Prefetch and Prerender: You do not like to wait, no one does. So, it is your moral duty to preload some pages of your website so that visitors would not have to wait. Just specify the URL that you want to preload with both these two tags and there you go.
Alt tag: Do not forget to add alt tag against all the images of your website. Since Google or other search engines cannot read images, you should always use alt tags against all the images of your website. This will increase the chances of your website appearing in google image search.
Page Load: Make sure that your website is not taking long time to get loaded. If your website takes more than 5 seconds to get loaded, it will cost you dearly. You might lose your visitors and a steady decline is what you are likely to see in the Google analytics report. To fix this thing, you need to follow certain rules religiously. You should not use large images no matter what. Do not use inline CSS or JS files as they contribute significantly to your website�s loading time. Create separate files and put all the codes therein. It will help you reduce page loading time to a great extent.
Read and Reread: Make sure that you have read all the content precisely. Typos are quite common these days and therefore, you should go through all the content of your website to minimize the chances of typos.
Sitemap: You need to have two versions of sitemap � HTML and XML. XML sitemap is for search engine submission purpose whereas HTML sitemap is for users who could otherwise unable to reach to some URLs of your website.
Robots.txt: Robots.txt is a simple txt file that needs to be placed at the root folder. It gives search engines the direction which pages you want them to crawl and which you want them exclude from their index. Just use the Disallow and Allow tags judiciously and there you are done.
If you have checked all of the above mentioned points, I can dare say that your website is in good shape and it is the time to make it live.
Author Bio
James Arnold is a passionate blogger. He has been writing articles on different promotional codes at coupon blogs where you can find discount for laithwaites wineand zagat wine promo code. He is a regular writer for a coupon website that has amazing offer on zagat wine coupon, laithwaites wine promo code and other promotional code.
Image source: yourseotips.com
 Public relations (PR) play an important role in promoting image of an organization. PR department is the connection between the public and organization which utilizes various media. With the changing times, the way PR is handled is also changed. All old-cum-traditional PR practices are to be revised or replaced with the new social media methods.
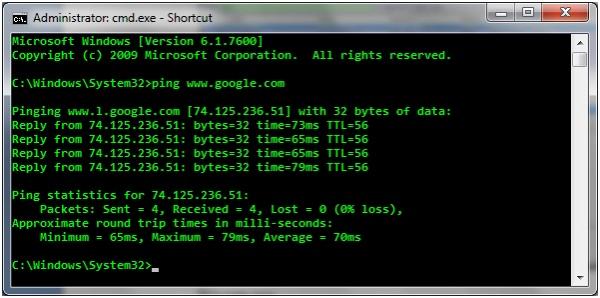
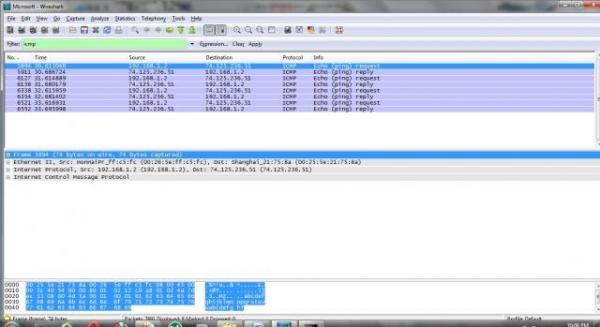
Public relations (PR) play an important role in promoting image of an organization. PR department is the connection between the public and organization which utilizes various media. With the changing times, the way PR is handled is also changed. All old-cum-traditional PR practices are to be revised or replaced with the new social media methods. We all are aware of PING command, hardly any person has not used this command using computer in day to day life but there are lot of this you may not be aware of . So, I’ll be going to take you deep into the "PING" command .
We all are aware of PING command, hardly any person has not used this command using computer in day to day life but there are lot of this you may not be aware of . So, I’ll be going to take you deep into the "PING" command .